top of page
Search

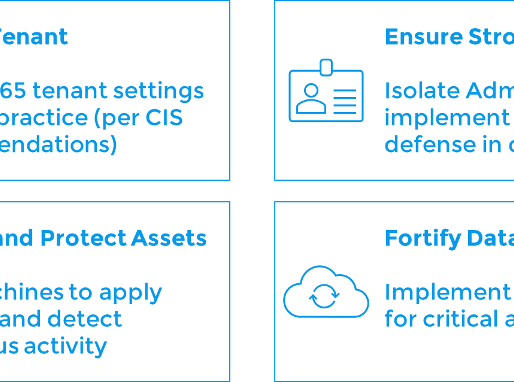
Hardening Your Microsoft 365 Tenant: A Practical Four-Pillar Approach
Setting up a Microsoft 365 (M365) tenant is often straightforward, thanks to the quick-start wizards. While ease and convenience are great, they don't always translate into strong security. When we created TBDCyber, we set up our M365 tenant in a matter of minutes. We had immediate access to all the productivity applications we needed, from Outlook to Teams. We had all the ease and convenience we needed to start operating our business, but the next question was: Are we doing
Jan 264 min read


What actually makes a data security program effective?
What actually makes a data security program effective? It’s not just about inventories or visibility dashboards—it’s about reducing...
Jul 22, 20251 min read


Insider Threat Management - Where to Begin?
In this short video, Justin Barnett breaks down three essential steps to help organizations build a strong foundation for their Insider...
Jul 22, 20251 min read


Rethinking Data Security: The Power of DSPM & Vulnerability Management
In this short video, our CISO, Zach Luze, breaks down how DSPM: Maps your sensitive data across repositories Connects with vulnerability...
Jul 17, 20251 min read


Thinking About DSPM? 8 Crucial Considerations Before You Buy
Author: Zach Luze, TBDCyber CISO and Director of Data and Security Architecture Data Security Posture Management (DSPM) is generating...
Feb 3, 20253 min read
bottom of page